Cyber Safe: UA Little Rock creating awareness of online safety
June 20-26, 2022
By Angelita Faller
With America experiencing an unprecedented increase in cyberattacks and malicious cyber activity, internet safety is becoming more important every day. In 2021, a record number of more than 847,000 complaints of cybercrime were reported to the FBI by the public, with potential losses exceeding $6.9 billion, according to the FBI’s Internet Crime Report 2021 found here: Cyber Sale PDF
June is recognized as National Internet Safety Month. It brings together nonprofit organizations, industry leaders, and federal and state governments to educate people to promote safe online behavior and responsible practices. At the University of Arkansas at Little Rock, faculty, staff, and students across the campus are engaged in efforts to arm citizens with important knowledge that can protect users against cybercrimes.
Helping Small Business Owners Thwart Cyber Attacks
In a joint effort to inform small business owners about online dangers, the Arkansas Small Business and Technology Development Center teamed up with the UA Little Rock Cyber Arena to create the Cyber Safe: Cybersecurity for Small Business online training course.
The free, self-paced online training is available at asbtdc.org/cyber-safe. The course complies with the federal government’s CMMC cyber standards, which helps small businesses compete for federal contracts that require cyber certification. CMMC is designed to protect sensitive unclassified information that is shared by the Department of Defense with its contractors and subcontractors.
“Our goal is to help small businesses protect themselves and their customers,” said ASBTDC State Director Laura Fine. “Cybercrimes are costly, and businesses need to have cybersecurity safeguards in place just like they have locks on their doors and other physical security measures. In fact, the Cyber Safe training shows that door locks are one element of cybersecurity.”
Cyber Safe contains six modules varying from 8-25 minutes in length that cover cybersecurity basics, access control, passwords, physical security, and network protection. CMMC cyber standards recommend that businesses should educate employees about the importance of setting strong passwords, recognizing malicious links, and installing the latest security patches, since most cyber incidents occur because of user error.
Tracking the Spread of Misinformation and Toxicity Online
Dr. Maryam Maleki, a May graduate with a Ph.D. in systems engineering, is one researcher with the Collaboratorium for Social Media and Online Behavioral Studies (COSMOS) who is studying how misinformation spreads online following models that predict the spread of infectious diseases.
“My research is focused on spreading misinformation on social media, especially Twitter,” she said. “I used my background in systems engineering to develop mathematical models and statistical analyses to evaluate the spread of misinformation on Twitter. I also have a model for measuring the spread of toxicity. Policy makers and scientists who use these mathematical models can define strategies to protect their social media platforms and to help control the spread of misinformation and toxicity.”
Online toxicity includes rude, aggressive, and degrading attitudes and behavior that occur in online platforms.
“Toxicity can result in prohibiting free speech by insulting people, scaring them, and silencing them,” Maleki said. “It may be an insult, hate speech, or a threat. Whenever this toxic behavior can make people feel bad or uncomfortable, they may leave the platform because they do not feel safe enough to continue the discussion.”
How to Stay Safe Online While Working Remotely
The sudden onset of the COVID-19 pandemic in 2020 brought the abrupt closure of many offices and workplaces that resulted in a shift to remote work for millions of Americans. A 2022 report from the Pew Research Center said that roughly six-in-ten U.S. workers who say their jobs can mainly be done from home (59%) are still working from home all or most of the time more than two years after the pandemic began. This is in comparison to the 23% who say they frequently worked remotely prior to the coronavirus outbreak.
Brian Keltch, UA Little Rock’s chief information officer who has more than 30 years of experience working in information technology, said that this new era of working remotely can lead to security risks when employees don’t take the proper security measures for their home devices. Those who work from home are especially vulnerable to sophisticated phishing attacks via email and texts that impersonate co-workers and bosses.
“These attacks are no longer the ‘Banking request from a king in a foreign country’ email, but have become much more sophisticated and targeted,” Keltch said. “I might get a false email from my supervisor that tells me to purchase this software right away, and I need it tomorrow. If I didn’t validate it, I might go purchase it from an unknown provider or provide my account information. Knowing how to recognize and combat these phishing attacks is important.”
It can be hard for employees to identify these messages as false since they often come from someone they know, include the company’s logo and email addresses, and contain inside information that strangers shouldn’t know.
“Cyber criminals really count on what they call social engineering,” Keltch said. “It’s tricking individuals to provide information they shouldn’t provide or to allow something to be installed on their machine that shouldn’t be installed. They rely on connectedness. They peruse social media to understand who your boss is, who your friends are, and they use that information to gain your trust and try to take actions that will harm you.”
Another major concern for employers is ransomware attacks where hackers will lock a system, encrypt files, and demand a ransom payment in order to access the system again. The perpetrators of the ransomware attack often demand payment in cryptocurrency because it’s untraceable.
Keltch recommends several tips for how remote workers can protect themselves online:
• Strengthen your password hygiene. The most important step you can take to protect yourself is to not use personal information in passwords and repeat passwords for account logins. Instead, use passphrases and a password manager to keep your login information more secure.
• Secure your home devices by updating your computer’s operating system and set it to automatically accept security upgrades and patches, encrypt hard drives and other electronic storage devices, and use a virtual private network to encrypt data.
• Harden your home’s WiFi network by making sure your WiFi router has a unique and non-default password and that you have enabled WiFi encryption. Regularly update your router’s firmware and install patches.
Spreading the Word
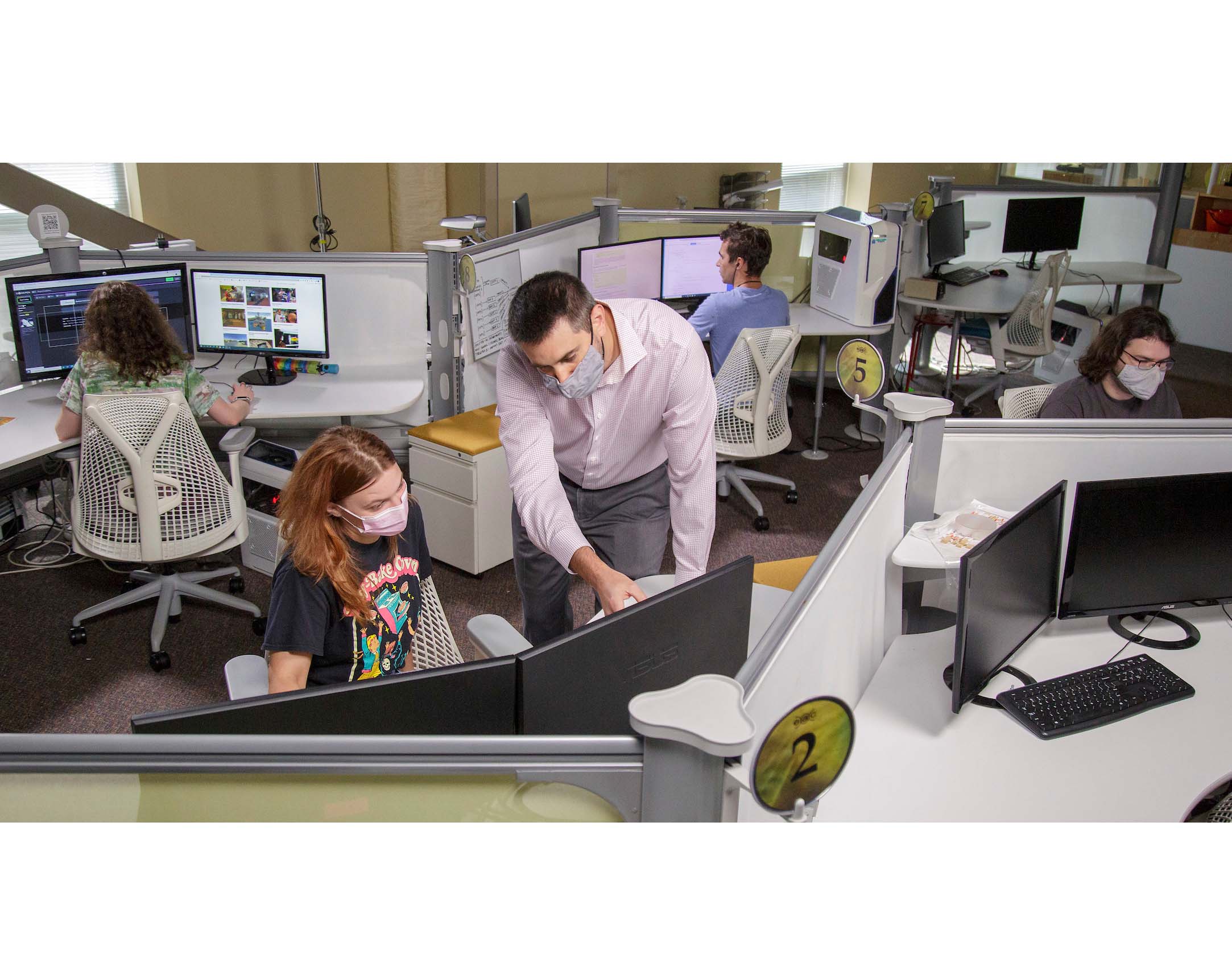
In the UA Little Rock Emerging Analytics Center found here https://ualr.edu/emerginganalytics/, researchers are often at the forefront of innovative research for virtual reality and interactive technologies. As experts in visualization, researchers decided that creating awareness of internet safety issues was the best way to keep the community informed about the issue that affects how many people every day.
A team of creative students from the Emerging Analytics Center used their skills to make Snapchat filters that the public can use to encourage the public to stay aware of their online actions and take steps to protect themselves.
Photo Captions:
1. Brian Keltch (top left), UA Little Rock’s chief information officer. Photo by Lonnie Timmons.
2. Jason Zak (top center), lead artist at the UA Little Rock Emerging Analytics Center, supervises students conducting virtual reality, augmented reality, and visualization research. Photo by Ben Krain.
3. Dr. Maryam Maleki (above) graduated from UA Little Rock in May with a Ph.D. in systems engineering. During her time as a researcher in the Collaboratorium for Social Media and Online Behavioral Studies, Maleki has been involved in high-profile research investigating the spread of misinformation and toxicity across social media. Photo by Ben Krain.
4. Dr. Nitin Agarwal, below left, Maulden-Entergy Endowed Chair and Distinguished Professor of Information Science at UA Little Rock, leads his team of student researchers in a discussion about analyzing possible threats from social media data at the Collaboratorium for Social Media and Online Behavioral Studies. Photo by Lonnie Timmons.
5. Arkansas Small Business and Technology Development Center State Director Laura Fine leads a group meeting of ASBTDC employees who are discussing how to help small business owners. The ASBTDC created the Cyber Safe learning course in conjunction with the UA Little Rock Cyber Arena to help small business owners learn about online dangers. (Photo by Ben Krain.)